Malware deployed in modern cyberattacks now primarily uses protection systems called packers to deceive antivirus tools.
These protections often cause antivirus engines to poorly characterize threats, which can lead to:
- False negatives, allowing malware to slip through defenses with potentially destructive consequences;
- False positives, generating extra alerts that burden security teams and slow operations;
- Incorrect characterizations, where an identified threat doesn’t reflect reality and can mislead analysts or responders.
1. What Is a Packer in Cybersecurity?
Packers (or crypters) are used to encrypt sensitive information within software and can also compress programs in order to optimize disk space. They are primarily employed to conceal a program’s code and functionality—either to protect intellectual property in the case of legitimate software, or to evade detection and hinder analysis in the case of malicious software.
However, packers are also widely used by hackers to conceal malware that will only be decompressed and de-protected at the time of execution.
It should be noted that the majority of antivirus solutions currently available on the market struggle to accurately identify the malicious nature of unknown software protected by a packer.
Given the complexity of this field, the purpose of this article is to clarify the various aspects involved.
2. Antivirus Solutions Poorly Characterize Software Protected by Packers
Antivirus solutions, as well as many analysis methods—even those based on artificial intelligence—struggle to accurately characterize software protected by packers. These characterization flaws can mislead analysts or result in false positives.
In this article, we examine the following example: a legitimate file called “hostname.exe”, a well-known component of Windows systems, compressed using the “JDPack” packer.
On VirusTotal, most antivirus engines incorrectly raise an alert, classifying this file as a threat (“malicious”, “trojan”, etc.). A few engines indicate the presence of a protection mechanism but still label the software as malicious. However, this packer can be used on both benign and malicious files.
This example highlights both the issue of false positives and the broader problem of poor threat characterization by antivirus solutions when dealing with protected files.
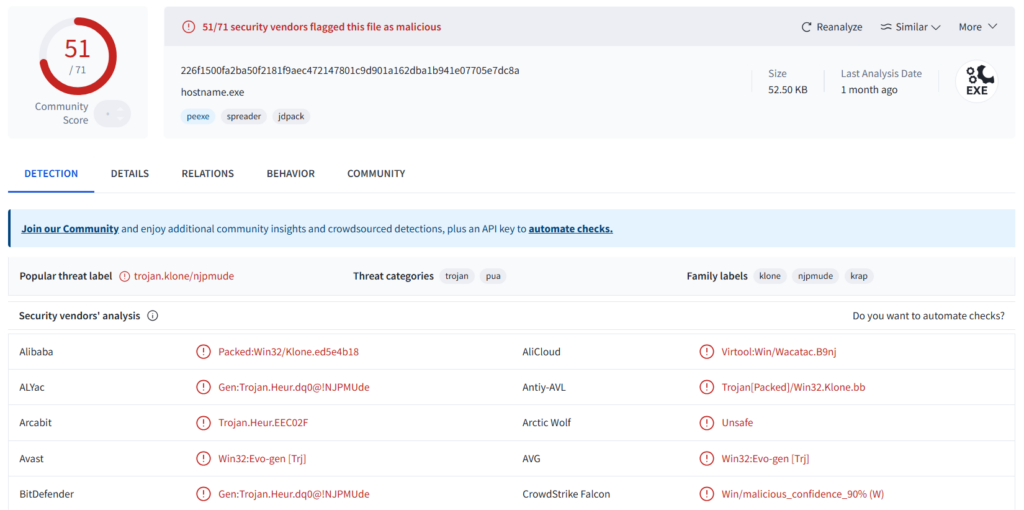
Figure 1: VirusTotal results for a “hostname.exe” file packed with the “JDPack” packer – Virus Total Link
3. Impact on Alert Management Within Your EDR/XDR
Protected benign files can lead to an increase in alerts within a SOC.
This forces analysts to perform additional checks on these files, resulting in a significant loss of time. In the case of a malicious file that is poorly characterized, analysts will also lose time, as they will not be able to identify the actual threat or accurately assess its level of severity.
An overload of irrelevant alerts severely reduces SOC efficiency. Analysts spend most of their time triaging false positives and may ultimately miss real threats.
This situation can also degrade key performance indicators such as MTTD (Mean Time To Detect) and MTTR (Mean Time To Respond) by extending detection and response times, thereby increasing overall risk exposure.
Relying on tools that poorly characterize threats not only slows down alert handling, but also prevents rapid doubt resolution.
In many cases, deeper analysis becomes the only option—often involving costly processes such as full sandbox execution or even reverse engineering.
4. Accuracy of Our Gorille Antivirus Tool in Detecting and Characterizing Packers
The previously presented case is a false positive, which is problematic as it requires manual handling by a SOC analyst.
When antivirus solutions are unable to go further in their analysis, it would be preferable for them to indicate that a protection mechanism has been detected but that the protected payload cannot be characterized. In its current form, this type of result does not provide sufficient information for SOC analysts to properly assess the threat.
The “Hxor” packer is an openly available packer used by multiple actors, both legitimate and malicious.
In this section, we examine two examples: a benign file (hostname.exe) packed with Hxor, and a malicious file (Akira) also packed with Hxor. This packer therefore illustrates both a false positive case and a mischaracterization case.
We analyzed these samples using VirusTotal and Gorille to demonstrate Gorille’s strength in detecting and characterizing packers, as well as its ability to access the file hidden behind the protection.
VirusTotal analysis of hostname.exe packed with Hxor
Hxor Hostname (60 detections) (Figure 2):
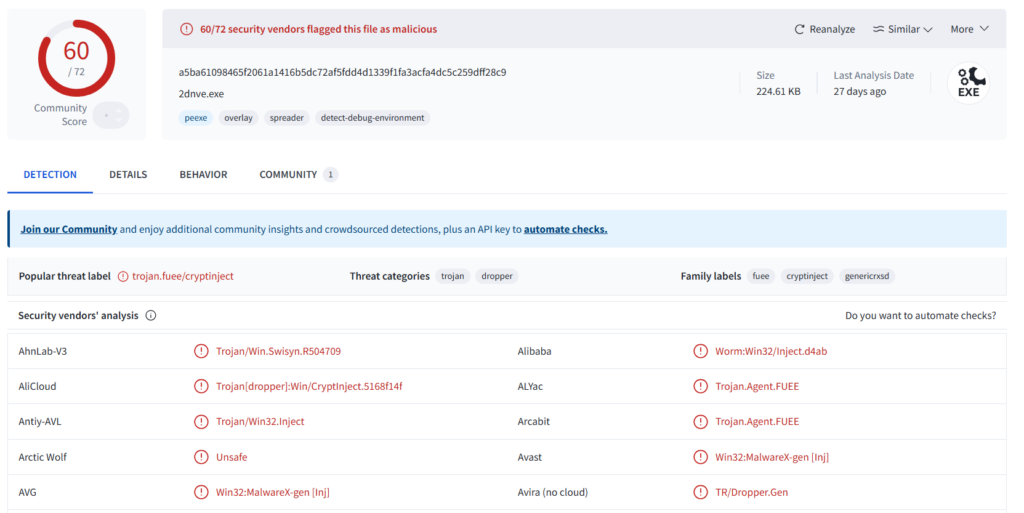
Figure 2: VirusTotal result for a “hostname.exe” file packed with “Hxor”– Virus Total Link
Hostname (0 detection) (Figure 3) :
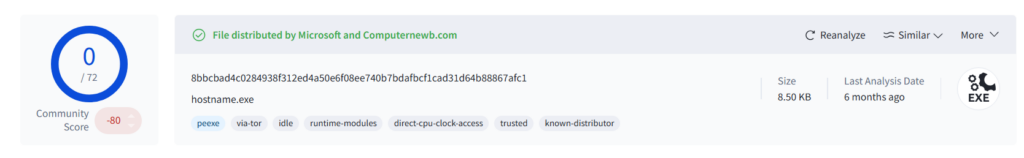
Figure 3: VirusTotal result for a “hostname.exe” file – Virus Total Link
In the case of a benign file (hostname.exe) packed with the Hxor packer, all antivirus engines classify it as malicious.
Let us now examine the case of the Akira malware packed with Hxor:
VirusTotal analysis – Hxor Akira (54 detections) (Figure 4):
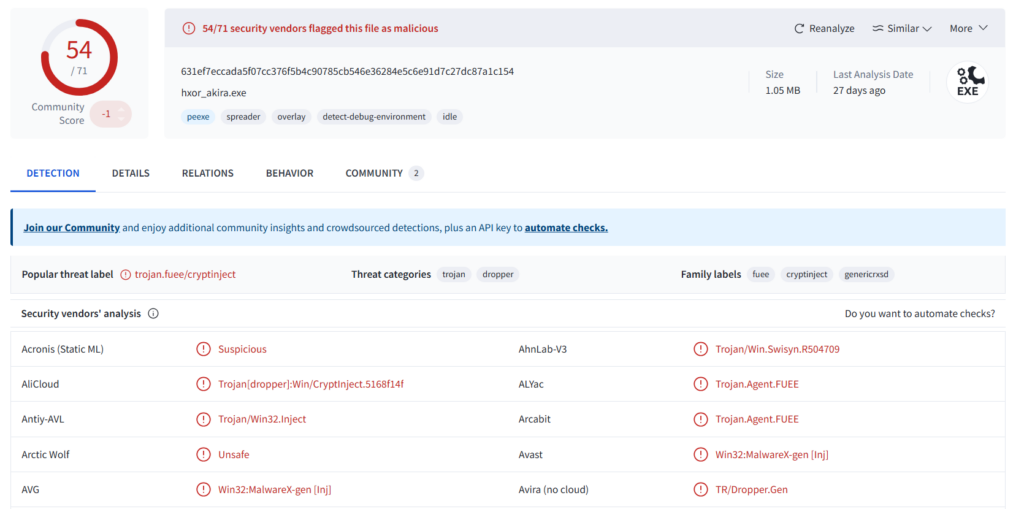
Figure 4: VirusTotal result for an “Akira” file packed with “Hxor” – Virus Total Link
Akira (61 detections) (Figure 5) :
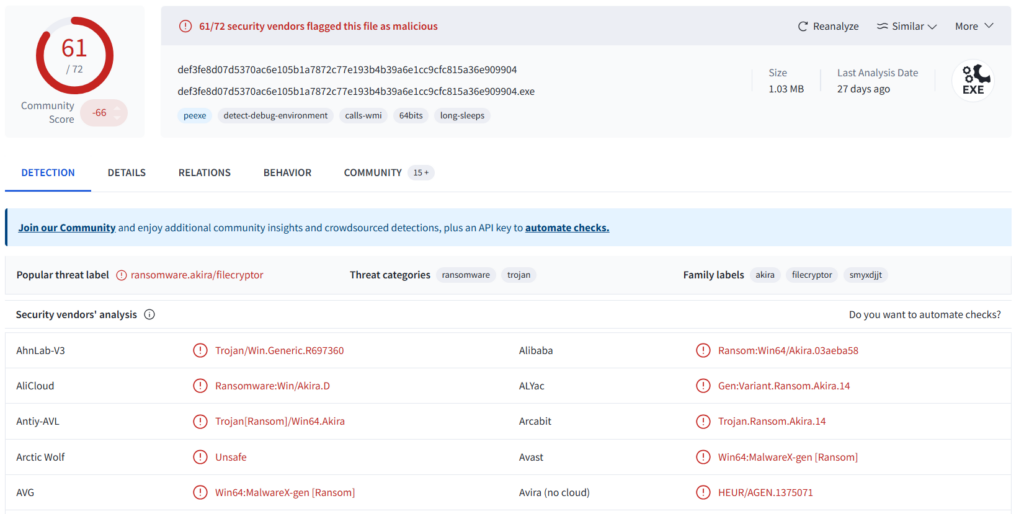
Figure 5: VirusTotal result for an “Akira” file – Virus Total Link
In the case of a malicious file (Akira) also packed with the Hxor packer, antivirus solutions detect the same behavior as in the previous case. They fail to access the malicious payload hidden behind the packer and therefore cannot effectively characterize the threat.
One of the key strengths of the Gorille solution and its packer detection engine is its ability to provide analysts with clear explainability of its results.
The Gorille solution performs in-depth analysis through multiple unpacking procedures designed to bypass protection mechanisms.
To achieve this, we have developed a complete deobfuscation workflow (Figure 6) and rely on a range of packer extractors, from highly specific to more generic ones.
Gorille is also equipped with a dynamic analysis engine capable of executing the software in order to trigger unpacking and remove protections.
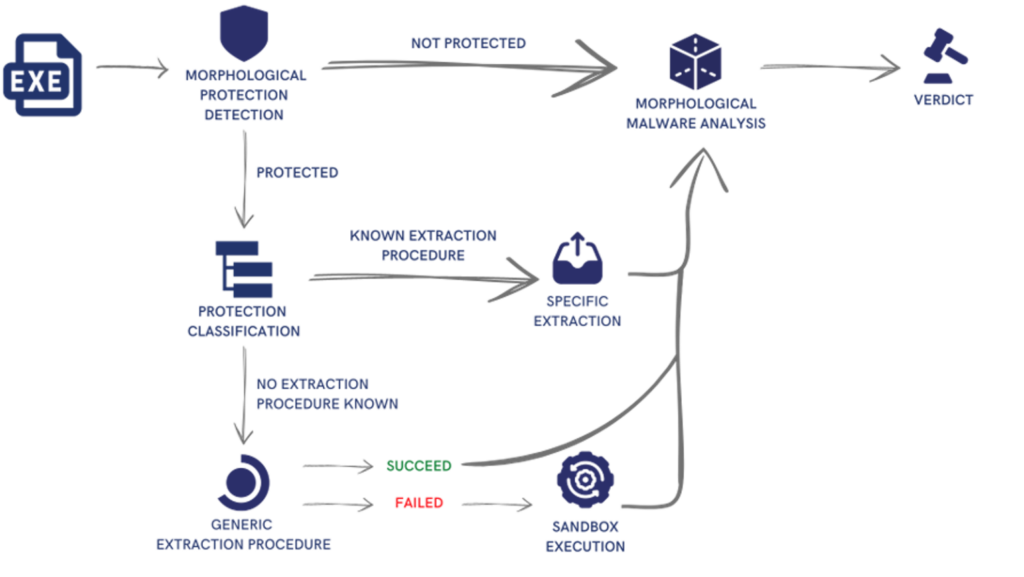
Figure 6: Gorille Workflow
Revisiting the previous examples (the JDPack-packed hostname.exe from Section 2 and the two Hxor-packed samples from Section 4), and analyzing them with Gorille, we can observe that Gorille is able to directly identify the packer and then leverage its internal unpacking methods to extract the packed file and analyze its payload.
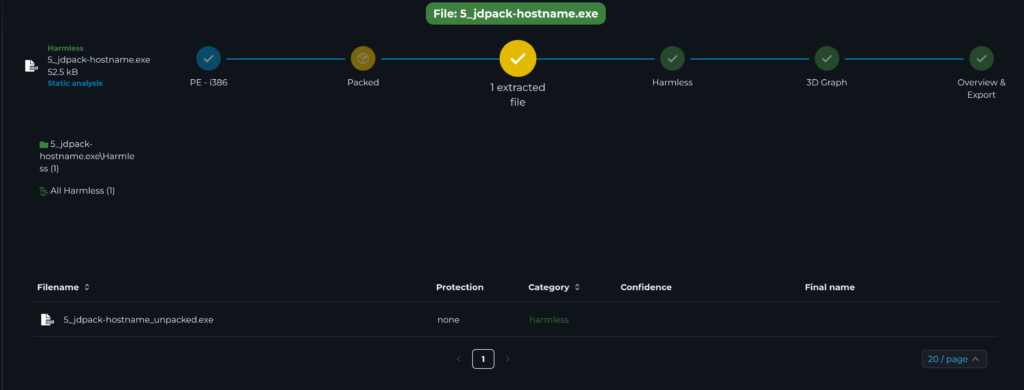
Figure 7: Gorille interface following the analysis of the JDPack-packed hostname.exe file
Gorille is also able to unpack Hxor, recover the hostname.exe and Akira files, and rely on its analysis to accurately characterize the threat (Harmless for hostname.exe and Malicious for Akira).
These analyses take an average of around fifteen seconds and are significantly less costly than dynamic analysis.

Figure 8: Gorille interface following the analysis of the Hxor-packed hostname.exe file

Figure 9: Gorille interface following the analysis of the Hxor-packed Akira file
Conclusion
Packers represent a central challenge in malware analysis.
Ubiquitous and increasingly sophisticated, they complicate detection, slow down investigations, and degrade security teams’ ability to quickly assess threats.
As a result, rapidly and accurately identifying and characterizing these concealment mechanisms has become a major challenge.
By automating the detection of packers and software protections, Gorille goes beyond simple alerting: it provides deep insight into binary behavior, accelerates analysis phases, and significantly reduces the time spent on protected samples.
Even when protections cannot be fully removed, Gorille delivers actionable and exploitable indicators to SOC analysts, facilitating decision-making and guiding investigations.
In a context where speed, accuracy, and automation have become critical for CERTs and SOCs, Gorille stands out as a key lever for strengthening operational efficiency against modern malware.
Would you like to see how Gorille concretely improves the detection and analysis of protected malware?
Schedule a personalized demonstration and discover how Gorille can be seamlessly integrated into your existing tools and processes.
IOCs :
| Hostname JDPack | 5600f93d771747dcff81af8adb8bfa1b |
| Hostname extracted | b1fba6647af3efe2898dfa53cd7b349b |
| Hxor Hostname | 021ca448570f803bf71e3b0f1ece1e67 |
| Hostname | b3a44f80f5b23c1f698398f5d49fffa6 |
| Hxor Akira | eb541d99f28dcdba52c887ae40b7aab8 |
| Akira | ae454079c93a7a1ce276756b9d62d196 |