The JDownloader website was compromised in early May 2026 and distributed a modified version of the Windows and Linux installers of JDownloader (https://www.bleepingcomputer.com/news/security/jdownloader-site-hacked-to-replace-installers-with-python-rat-malware/), a Supply-Chain attack. This type of supply chain compromise attack is particularly formidable, as it exploits the legitimacy of the official website to infect unsuspecting users.
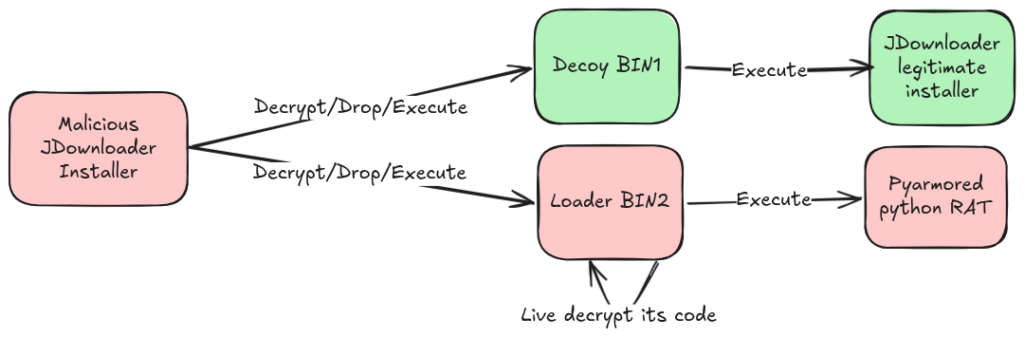
The compromised versions of the JDownloader installer contain a loader (stage 2) that executes a Python RAT (stage 3) after disabling the antivirus software on the infected machine.
Attack summary
We present here an analysis of this malware (md5: d3b398a757b424f91e645985ade00516)based on the results of our Gorille analysis engine. Gorille will verify the integrity of JDownloader installers by comparing functionalities with previously identified malicious functionalities.
Identifying the malicious function with Gorille
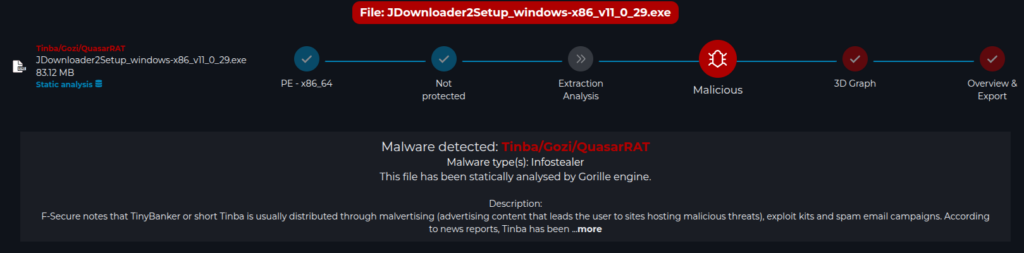
Main view of Gorille analysis
The installer is detected by Gorille as sharing common code with several different malware. It successfully identified a malicious modification of the JDownloader installer. https://demo.gorille.tech/file/detail/6a0483aafa6bd8c8ea7e71a4?publicToken=EDzRHRCguQnhVVUeB6b5ECJ_uqlVTGJjZYbWZLfAxOQ
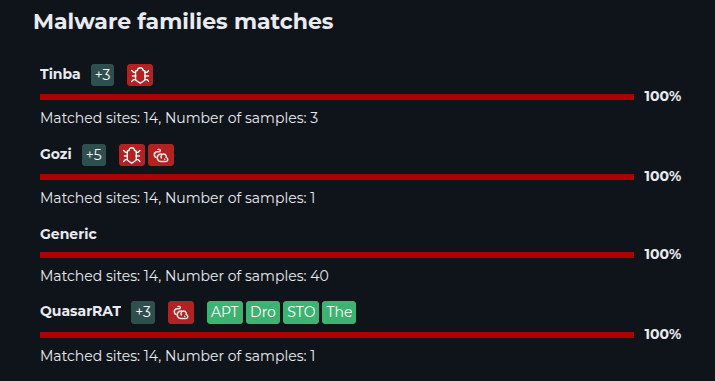
Description of similarities in Gorille analysis
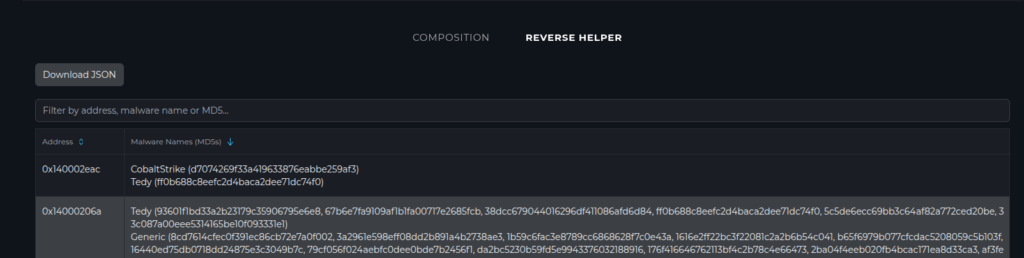
Display of Gorille similarity addresses – reverse engineering aid
Gorille analysis goes further by targeting the problematic functionality in the compromised JDownloader installer code. To do this, simply list the addresses identified as malicious code. These addresses in the compromised JDownloader installer code target a very specific area of the installer: the sub_1400019e0 function.
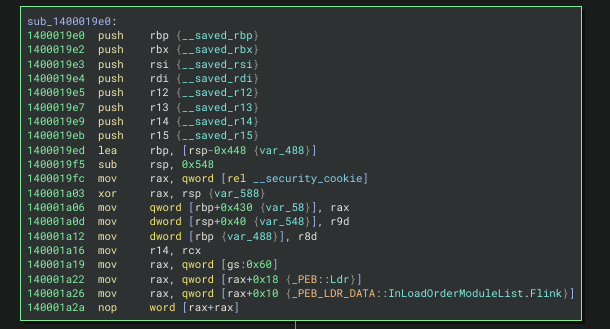
Malicious function in the JDownloader installer
This function notably performs a PEB walk to hide API calls — a highly suspicious behavior common to many malware — that Gorille is capable of detecting. This function notably performs a PEB walk to hide API calls — a highly suspicious behavior common to many malware — that Gorille is capable of detecting.
Gorille put us on the right track to begin analysis
The explainability of Gorille results allows us to retrieve the exact locations it considers suspicious, enabling the function to be linked to functions that may have already been analyzed by reverse engineering teams. Here we immediately identified the API hashing function through similarity with other malware using the same type of functionality.
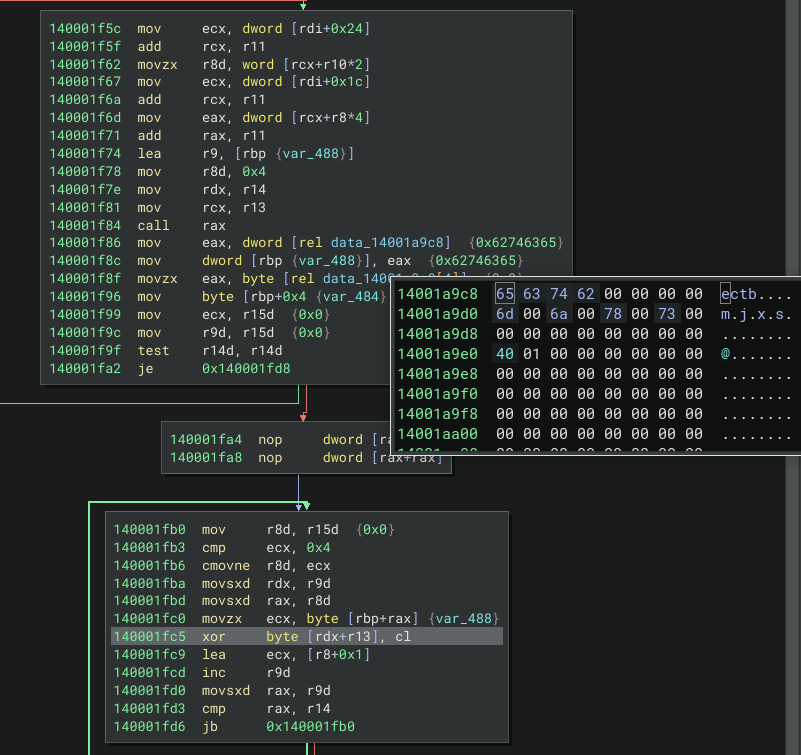
In this sub_1400019e0 function, we distinguish hidden calls to APIs, notably WriteFile and ShellExecute. We also identify a decryption loop: an xor that decrypts two files with the key ectb
- A file “BIN1”, legitimate file that launches the legitimate JDownloader installer
- A file “BIN2”, the stage 2 loader that is dropped in Temp. This loader disables several antivirus programs and launches the Python RAT.
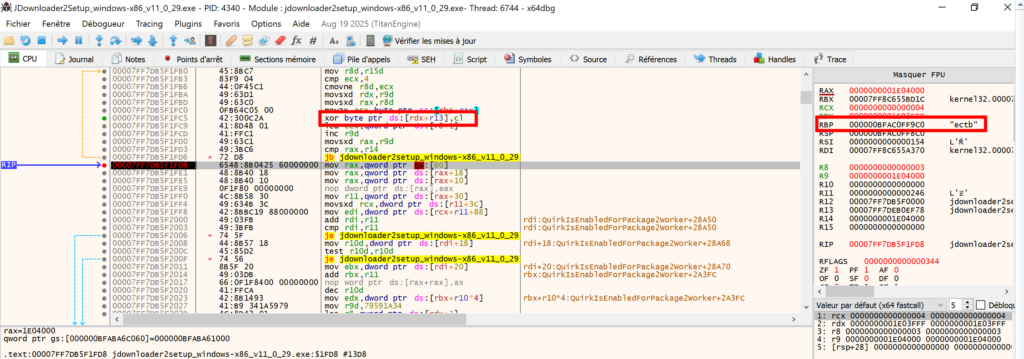
Stage 2 Loader decryption loop
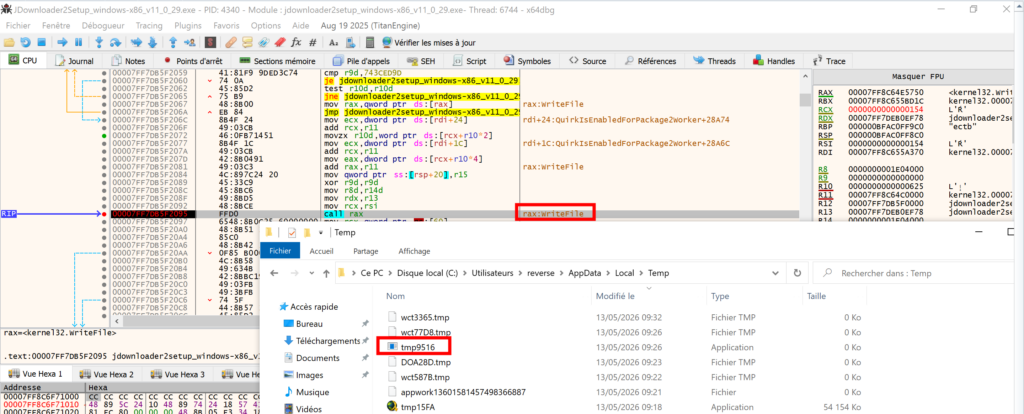
Writing the temporary file containing the Stage 2 Loader
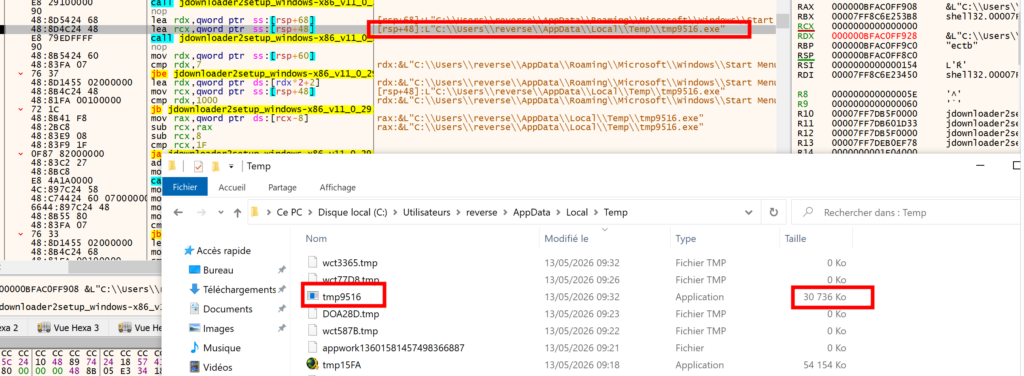
Stage 2 Loader execution
Once executed, the strings corresponding to the registry and Python script launch are decrypted on the fly with the key: fywo
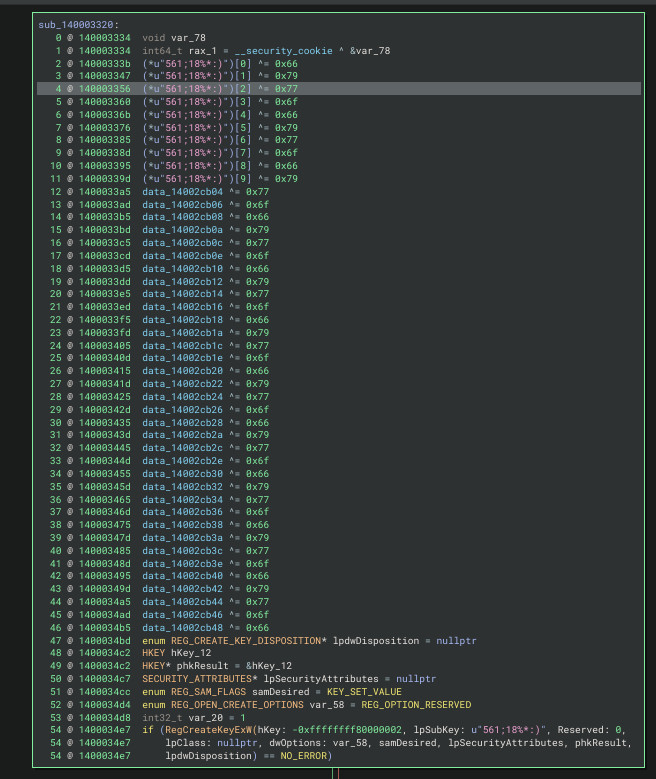
Encrypted strings in the Stage 2 Loader code
Once decrypted, we distinguish the following strings :
sub_140003320
Registry Manipulation, Deactivate Real-Time protection, ...
SOFTWARE\Policies\Microsoft\Windows Defender
DisableAntiSpyware
SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection
DisableRealtimeMonitoring
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\Account protection
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\App and Browser protection
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\Device performance and health
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\Family options
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\Firewall and Network protection
SOFTWARE\Policies\Microsoft\Windows Defender Security Center\Virus and threat protection
\Policies\Microsoft\Windows\WindowsUpdate
The stage 2 loader installs its own “pythonw.exe” interpreter and installs various libraries for the malicious Python script, notably cryptography and request which will be used to contact the C2s.
The loader executes the malicious Python script packed by PyArmor
unk_14002eff0 (Installation RunTime)
\pythonw.exe -m pip install --timeout 30 --retries 99999 -U pywin32 cryptography msvc-runtime gevent requests requests[socks]
sub_14000ADD0 runPython:
PYTHON314_INSTALLER
/quiet Include_tcltk=0 Include_test=0 Include_doc=0 Shortcuts=0 AppendPath=1
C:\Program Files\Python314
BIN1
BIN2
BIN3
\Lib\runtime.py
\Lib\pyarmor_runtime_000000
\Lib\pyarmor_runtime_000000\__init__.py
\Lib\pyarmor_runtime_000000\pyarmor_runtime.pyd
pythonw.exe
HKCU\SOFTWARE\PythonAssessment of using Gorille to detect Supply-Chain attacks
Gorille is an effective tool in this Supply-chain attack context, allowing as shown here to immediately identify the JDownloader compromise. But it also goes further to accelerate the analysis of the compromise, which is an essential step to understand the real impact of the attack on systems that downloaded the compromised version of JDownloader.
IOCs
| d3b398a757b424f91e645985ade00516 | Compromised JDownloader installer (Windows version) |
| 0721d27c2530ee11b92ed67d8aae29be | Loader stage 2 (BIN2) |
| parkspringshotel[.]com/m/Lu6aeloo.php auraguest[.]lk/m/douV2quu.php 172.96.172.91 209.133.215.178 | C2 servers |
References
Gorille analysis of the corrupted JDownloader installation program :
Article about this attack
People who also shared their analysis of this malware when we completed writing this article :
PyArmor key extraction